BestCrypt 8.23 review
DownloadBestCrypt creates and supports encrypted virtual volumes for Linux
|

|
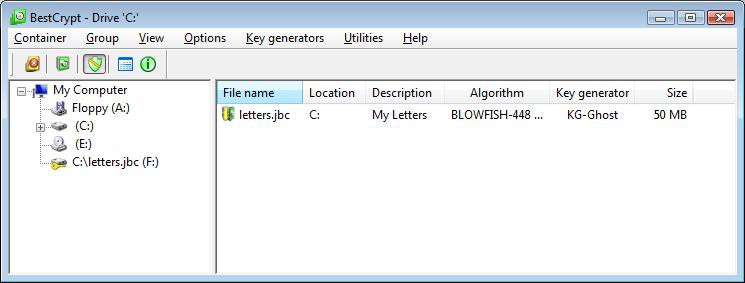
BestCrypt creates and supports encrypted virtual volumes for Linux. BestCrypt volume is accessible as a regular filesystem on a correspondent mount point.
The data stored on a BestCrypt volume are stored in the container file. A container is a regular file, so it is possible to backup, move or copy it to other disk (CD-ROM or network, for instance) and continue to access encrypted data using BestCrypt.
BestCrypt supports the following encryption algorithms: GOST (256-bit key) in Cipher Feedback mode and RIJNDAEL (256-bit key), IDEA (128-bit key), Blowfish (256-bit key), Blowfish-448 (448-bit key), Blowfish (128-bit key) DES (56-bit key), Triple DES (168-bit key), CAST (128-bit key), TWOFISH (256-bit key) in Cipher Block Chaining mode.
In general, installation and using BestCrypt for Linux is very easy:
Installation.
Please note that kernel sources are required to build and install BestCrypt for Linux.
If your Linux distribution supports RPM, download .src.rpm version of BestCrypt for Linux. Then rebuild
rpm --rebuild BestCrypt-x.y-z.src.rpm or
rpmbuild --rebuild BestCrypt-x.y-z.src.rpm on newer systems and install it
rpm -i /usr/src/redhat/RPMS/i386/BestCrypt-x.y-z.i386.rpm
If your Linux distribution does not have RPM, you should download .tgz version of BestCrypt distributive. In order to install, unpack it into separate directory and run there
make
and
make install
BestCrypt 8.23 keywords